Enterprise AI risks rarely begin with catastrophic system failures. Most begin quietly inside workflows that appear to be functioning normally. Hidden enterprise AI risks include automation bias, model drift, prompt injection, shadow AI, opaque workflows, weak governance and dependency failures across connected systems. These risks often develop inside approved enterprise…
Explore our latest insights
In 2025, we find ourselves at the cusp of a significant shift in how we interact with technology. While screens have been the cornerstone of our digital lives for decades, the rise of Zero UI is quietly revolutionizing the way we engage…
From predicting diseases before symptoms appear to creating personalized shopping experiences, AI is revolutionizing healthcare, retail, finance, manufacturing, and marketing. But with great power comes great challenges. How do we ensure data privacy? How do we address ethical concerns? And what happens…
Salesforce dashboards are powerful tools that give a visual representation of your business data, enabling better decision-making and strategy development. Whether you're a sales manager, marketer, or executive, dashboards can help you monitor key performance indicators (KPIs), track goals, and enhance your…
You’ve probably seen posts about tools like Claude Code generating working features in minutes. The demos look effortless: prompt in, code out, done. The reality feels different when you try it yourself. Getting useful output takes iteration, clear intent and a solid understanding of what you’re building. Without that,…
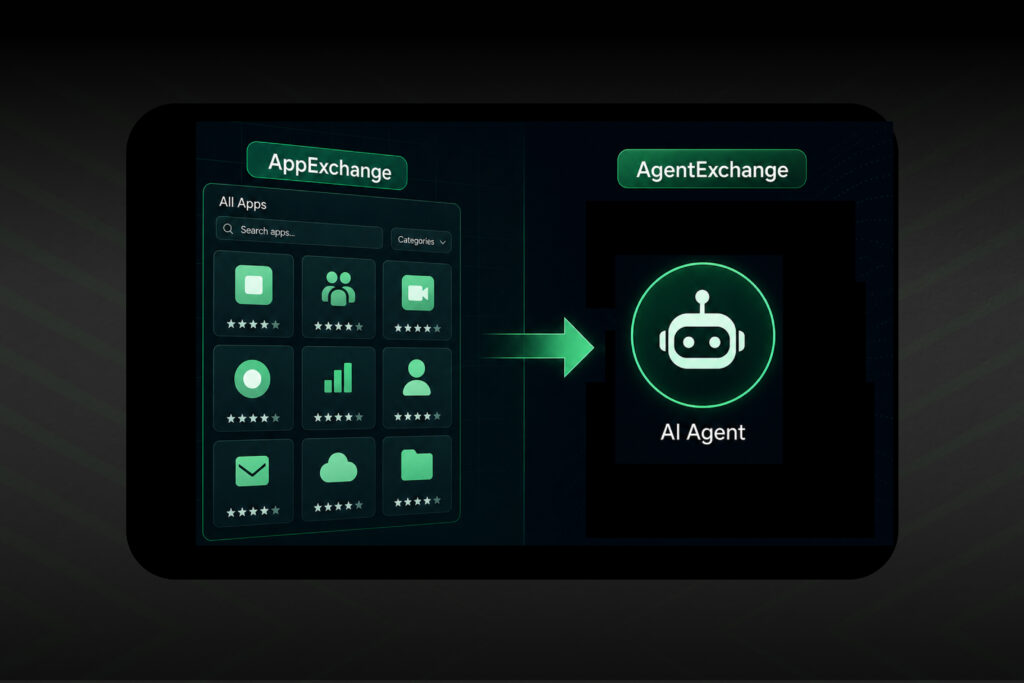
For over two decades, the Salesforce AppExchange has served as the bedrock of enterprise customization. With more than 5,000 ready-to-install applications, 80,000 peer evaluations and over 6 million installs, it became the primary marketplace where technology leaders extended Salesforce and addressed specific functional…
What is actually real, what is breaking in production and what the future of agentic AI looks like for enterprises that plan to get it right. Research drawn from: Gartner Hype Cycle for AI 2025, Deloitte Emerging Technology Trends 2025, McKinsey AI Survey late 2025, NIST AI Risk Management Framework 2025. …
The Software Development Lifecycle (SDLC) has adapted to every major shift in engineering. Agile improved speed, DevOps connected development and operations and cloud expanded scale and flexibility. Each transition refined execution. None fundamentally changed where decisions were made. However, Agentic AI does.…
The conversation around AI has grown quieter and more serious. A year and a half ago, AI discussions were full of pilots and proofs of concept. Teams explored possibilities, tested tools and experimented with ideas. That phase was necessary, but it was…
Over 80% of Salesforce customers have already transitioned to Lightning. If your organization is still operating on Classic, you're swimming against digital evolution. Salesforce is fully committed to Lightning, which makes Salesforce Lightning migration a business requirement, not a nice-to-have. While Salesforce…
The integration landscape has fundamentally transformed. What once meant connecting systems through APIs has evolved into something strategic: empowering autonomous AI agents to orchestrate intelligent workflows across entire enterprises. Salesforce MuleSoft integration solutions are now essential for organizations seeking to modernize operations.…
Healthcare systems aren’t overwhelmed because patients need more care; they’re overwhelmed because simple questions get stuck in phone queues and portals. Patients wait, staff gets buried in routine tasks and the gap between need and capacity keeps growing. Creating healthcare apps today…
Your checkout flow has a 68 percent abandonment rate. Users pause on the payment screen, hesitate, then disappear. The product manager blames the form. The developer wants fewer steps. But that pause isn’t about layout. It’s a moment of doubt: trust, returns…
Walk into any enterprise IT department today and you'll hear the same frustration. Teams are drowning in integration requests while business units wait months for simple data connections. The numbers tell a stark story: only 29% of enterprise applications can actually communicate…
Companies are rolling out AI agents at record speed; finance uses them to process invoices, marketing for campaigns and customer service to handle tickets. Each agent works well on its own, but most were never designed to collaborate. As more teams explore…
Dreamforce 2025, which took place just a few weeks ago, marked a clear inflection point for Salesforce and its ecosystem. Agentforce 360, Data 360 and Revenue Cloud are converging to define the Agentic Enterprise. Where AI agents don’t assist from the sidelines,…
Your development teams face an impossible choice every day: deploy fast with low-code platforms and hit walls when you need customization or build everything from scratch with pro-code development and watch weeks disappear into simple automation tasks. It's costing you more than…
Choosing a UI/UX design agency used to be simpler. That approach doesn't work anymore, even though you could just look at portfolios, meet a few creative directors, compare quotes and sign the one that "felt right." Every UI/UX design agency today claims…
No results found. Try a different search term.