For over two decades, the Salesforce AppExchange has served as the bedrock of enterprise customization. With more than 5,000 ready-to-install applications, 80,000 peer evaluations and over 6 million installs, it became the primary marketplace where technology leaders extended Salesforce and addressed specific functional…
Explore our latest insights
Over 80% of Salesforce customers have already transitioned to Lightning. If your organization is still operating on Classic, you're swimming against digital evolution. Salesforce is fully committed to Lightning, which makes Salesforce Lightning migration a business requirement, not a nice-to-have. While Salesforce…
The integration landscape has fundamentally transformed. What once meant connecting systems through APIs has evolved into something strategic: empowering autonomous AI agents to orchestrate intelligent workflows across entire enterprises. Salesforce MuleSoft integration solutions are now essential for organizations seeking to modernize operations.…
Walk into any enterprise IT department today and you'll hear the same frustration. Teams are drowning in integration requests while business units wait months for simple data connections. The numbers tell a stark story: only 29% of enterprise applications can actually communicate…
Companies are rolling out AI agents at record speed; finance uses them to process invoices, marketing for campaigns and customer service to handle tickets. Each agent works well on its own, but most were never designed to collaborate. As more teams explore…
Dreamforce 2025, which took place just a few weeks ago, marked a clear inflection point for Salesforce and its ecosystem. Agentforce 360, Data 360 and Revenue Cloud are converging to define the Agentic Enterprise. Where AI agents don’t assist from the sidelines,…
Salesforce isn’t broken; it’s being ignored. Every skipped update, every unused dashboard, every representative working in a personal spreadsheet quietly drains ROI. Salesforce adoption is an experience issue. And customer and employee experiences go hand in hand. When they’re designed together, they…
Salesforce promises visibility, efficiency and growth. Yet most executives share the same frustration “we invested heavily, we went live, but the results are not what we expected.” Adoption lags, sales teams slip back to old tools and the ROI conversation gets uncomfortable.…
For years, Salesforce optimization meant running a health check, fixing red flags, cleaning up unused objects and keeping the organization secure. While these steps still matter, today organizations are looking at how to optimize Salesforce AI to scale securely and efficiently.Let’s take…
AI is no longer something you can afford to “wait and see” on. It is here, it’s moving fast and Salesforce AI strategy isn’t sitting still. Between Data Cloud, Copilots and Agentic AI, they have made it clear that AI is baked…
Salesforce powers some of the world’s most successful businesses but building and maintaining a successful Salesforce setup takes more than adding a few automations or dashboards. Whether you’re customizing a CRM for internal teams, building a new SaaS product on the platform…
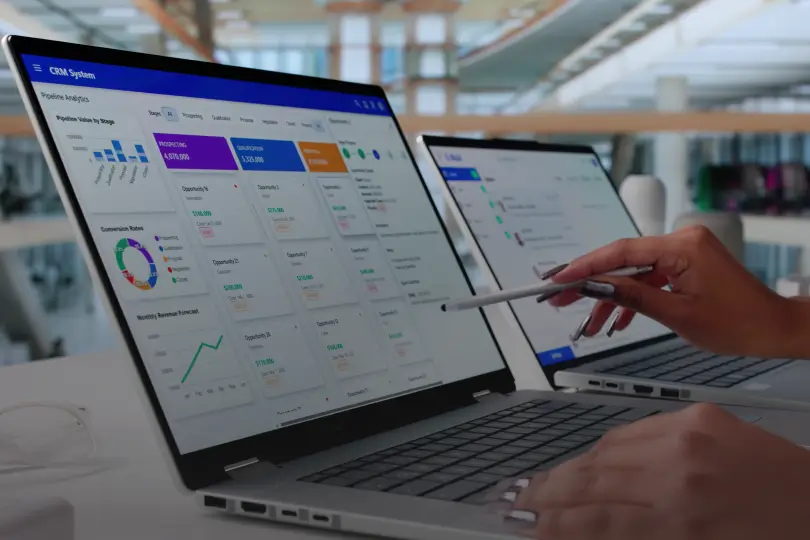
Salesforce has become the cornerstone of customer relationship management for enterprises across industries. It helps manage sales activities, customer service, marketing and more from a centralized cloud platform. However, despite its power, many business processes surrounding Salesforce services still rely heavily on…
In today’s competitive market, optimizing sales workflows is more than just a convenience; it’s essential for operational success. Sales teams often struggle with inefficient processes that can slow down productivity. This impacts conversion rates, and ultimately, hinders business growth. Salesforce offers a…
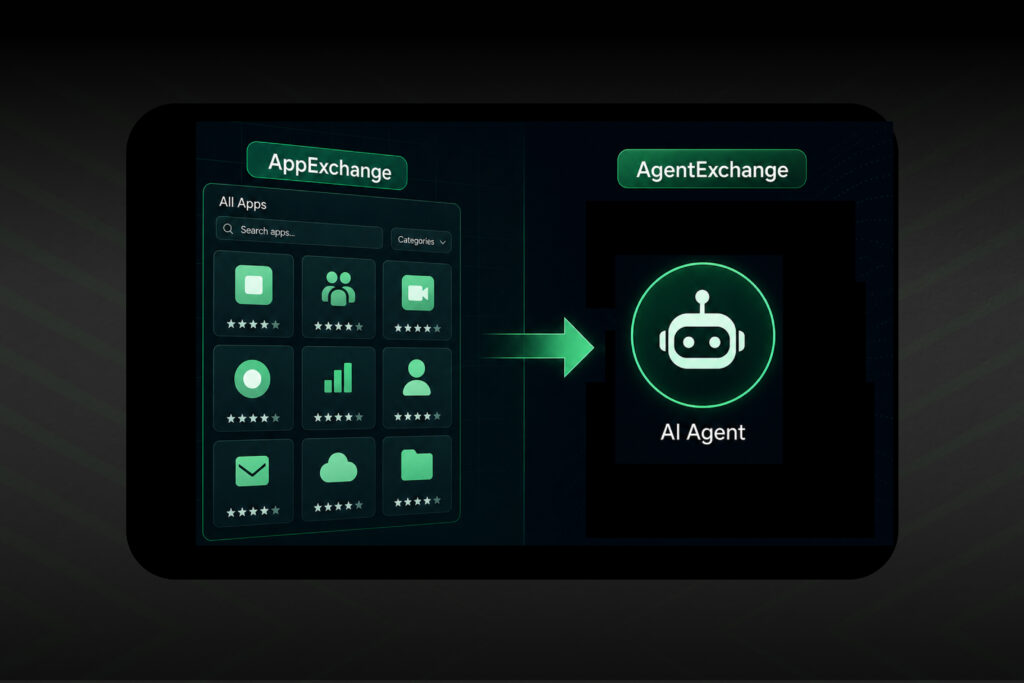
There’s never been a more exciting time to be in the Salesforce ecosystem. Over the years, AppExchange has helped thousands of enterprises streamline processes, extend CRM capabilities, and build high-performing systems—all without starting from scratch. It's a marketplace that shaped how businesses…
Let’s be honest; Salesforce automation has come a long way, but it still has its limits. We’ve all dealt with frustrating automated systems; chatbots that don’t understand us, processes that break down the moment something unexpected happens. Traditional automation is rigid; it…
No results found. Try a different search term.